Why US Enterprises Cannot Delay Java Modernization in 2026
The support cliff for legacy Java infrastructure has arrived faster than most CTOs anticipated. What seemed like distant deadlines two years ago are now immediate budget and risk management decisions:
- Oracle Java 8 ended public commercial updates in January 2019, forcing enterprises onto costly extended support or risky unpatched deployments [1].
- Oracle Java 7 extended support officially ended in July 2022, leaving systems running on completely unsupported runtimes [2].
- Jakarta EE introduced a mandatory namespace change from javax.* to jakarta.*, requiring code updates across frameworks, libraries, and application servers [3].
- Spring Boot 2.x OSS support ended in 2023. Spring Boot 3.3 OSS support ended in June 2025. Spring Boot 4.0 shipped in November 2025, requiring Java 17 minimum and Jakarta EE 11. Enterprises on Spring Boot 2.7 are now two major versions behind the current stable release.
The risk is not that your application stops running when OpenJDK 8 community support ends in November 2026. The risk is that when the next critical vulnerability is discovered in the runtime or a dependency, there will be no security patch available.
US enterprises running unpatched runtimes in SOC 2, HIPAA, or PCI-DSS environments face compliance audit failures independently of any security incident. Organizations rationalizing delay through vendor extended support contracts typically pay premium annual fees while accumulating compounding technical debt as the ecosystem continues to move ahead.
For enterprises, the risks of delay are now quantifiable:
- Operational Risk: Legacy and unsupported runtimes are among the leading security risks identified in IBM’s 2024 Cost of a Data Breach Report, with the average breach costing $4.88M.
- Compliance Exposure: Running unsupported Java versions creates audit failures for SOX, HIPAA, PCI-DSS, and GDPR compliance.
- Talent Scarcity: The average time to hire for EJB and Struts specialists now exceeds 120 days, with salary premiums reaching 40% above market rate for modern Java skills.
All this means Java modernization is now a defensive necessity to secure systems, control operational risk, and maintain development velocity in an increasingly cloud-native world.
In the sections that follow, you’ll find:
- A stack-by-stack migration map with recommended targets, alternatives, and hidden pitfalls.
- Economic impact data to build the executive business case.
- A decision framework for choosing the right modernization path for your enterprise.
- Risk and compliance triggers that demand immediate action.
- How Gen AI and automation can reduce migration timelines by 60% while improving code verification.
- Real-world case metrics from enterprise Java modernization projects.
By the end, you’ll have a data-driven view of what migrating to modern Java involves, what ROI it delivers, and how to execute with minimal business disruption.
Java Modernization ROI for Enterprise: TCO Analysis and Measurable Outcomes
For leadership teams evaluating capital allocation, Java modernization competes with every other strategic initiative. A credible business case must demonstrate clear, measurable returns across multiple operational areas.
Migrating to modern Java isn’t just about avoiding support fees. It fundamentally changes the economic profile of your application portfolio, from infrastructure efficiency and developer productivity to security risk and cloud optimization.
The Five Most Measurable Areas of Impact:
| Area | Pre-Migration Reality | Modern Java Outcome | Why It Matters |
| Infrastructure Cost | Over-provisioned servers to handle monolith inefficiencies, expensive application server licenses | 40–60% lower running costs through containerized Spring Boot with elastic scaling (Forrester) | Redirects budget from maintenance to innovation projects |
| Application Performance | Long startup times (2–5 minutes), heavy memory footprint, slow deployment cycles | 10x faster startup with GraalVM native compilation, 50% memory reduction with modern JVM | Improves user experience and enables real-time scaling |
| Security & Compliance | Unpatched vulnerabilities, legacy authentication, manual audit processes | Actively maintained frameworks with automated security scanning and compliance reporting | Reduces breach risk from $4.88M average cost to manageable operational expense |
| Developer Productivity | Manual builds, heavyweight IDEs, complex deployment procedures | Modern toolchain with automated CI/CD, containerized development, and cloud-native debugging | 3x faster feature delivery cycles, 60% reduction in defect rates |
| Talent Availability | Shrinking pool of legacy framework specialists, premium hiring costs | Access to modern Java ecosystem talent with 10x larger candidate pool | Eliminates delivery bottlenecks and reduces compensation premium |
Multi-Year TCO Analysis
A 3–5 year Total Cost of Ownership analysis shows enterprises modernizing legacy Java systems reduce total operational costs by 35–50% while improving system reliability and feature delivery speed.
Primary cost reduction drivers:
- Infrastructure optimization: 45% reduction in compute costs through containerization and right-sizing
- License elimination: $500K–$2M+ annually by moving from WebLogic/JBoss to embedded Spring Boot
- Operational efficiency: 60% fewer production incidents requiring manual intervention
- Developer velocity: 40% reduction in time-to-market for new features
For a detailed cost framework, see the 2026 Java modernization cost guide and the full ROI analysis.
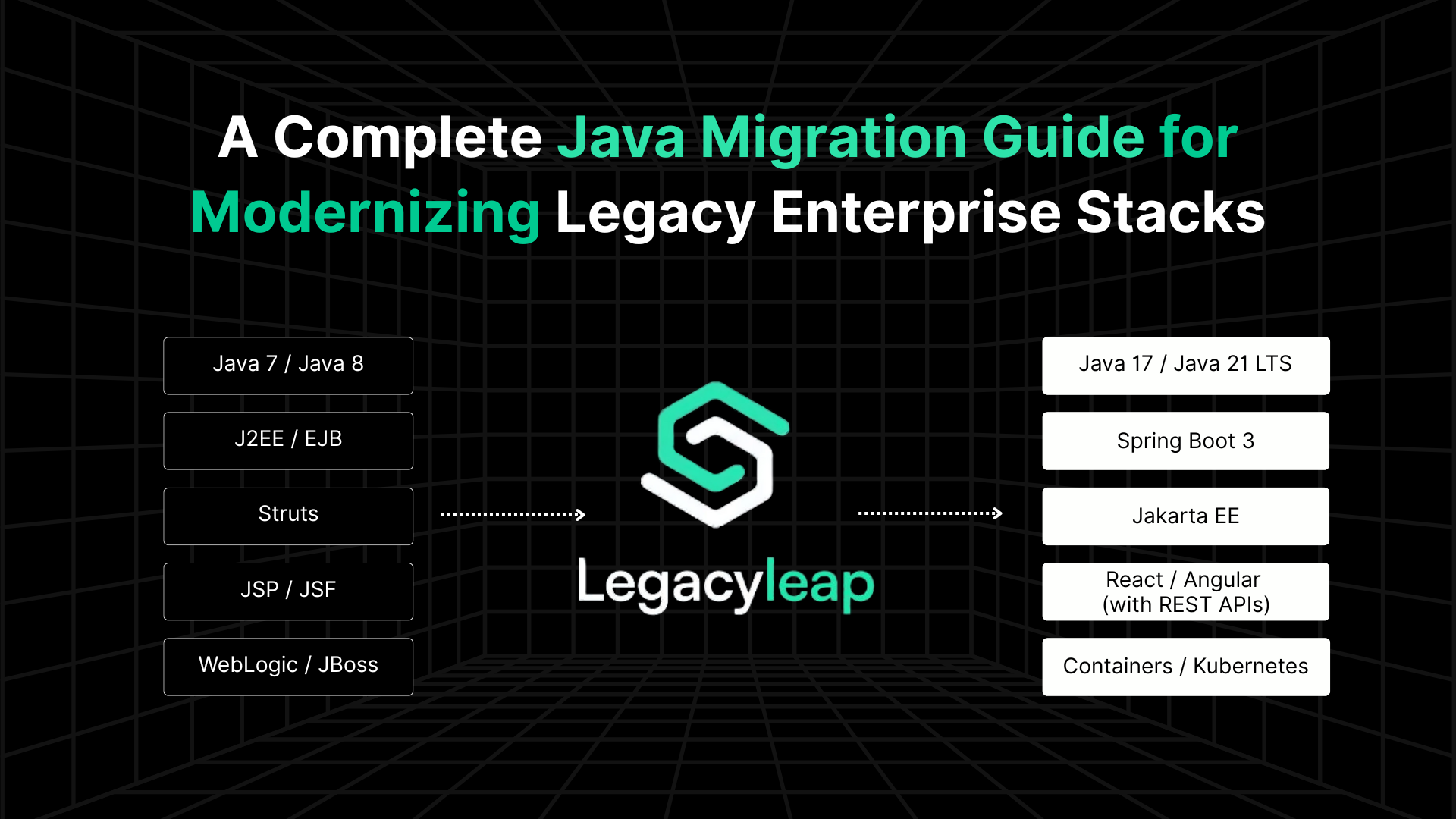
Java Migration Stack Map 2026: Legacy to Modern Targets Including Java 25 LTS and Spring Boot 4.0
Every migration decision starts with understanding exactly what you’re running today, when support ends, what business risks you’re accepting by staying, and what measurable outcomes you can expect from modernizing.
This reference table distills enterprise Java stacks into migration-ready intelligence: current state assessment, modern targets, support windows, common pitfalls, expected business outcomes, and ROI measurement points.
| Legacy Stack | Modern Target Stack | EOL/Support Status | Key Migration Pitfalls | Primary Business Outcomes | ROI Measurement Levers |
| Java 7 & Below | Java 21 LTS (minimum) or Java 25 LTS (recommended for programs initiating in 2026, Oracle support through 2033) | Java 7 extended support ended July 2022 | Legacy API dependencies, library incompatibilities, build system overhaul required | Supported runtime with 10+ years of updates, 40% performance improvement | Eliminated security patching costs, improved hiring pipeline |
| Java 8 on WebLogic/JBoss | Spring Boot 3.x or Spring Boot 4.0 with embedded Tomcat or cloud-native containers | Java 8 commercial support ended January 2019 | Vendor lock-in complexity, manual deployment dependencies, monolith coupling. Migration from Spring Boot 2.x to 4.0 requires a phased path through 3.5, with Jackson 3.x and Jakarta EE 11 as additional breaking dependencies. | Portable workloads, automated scaling, faster deployment cycles | 50% infrastructure cost reduction, 3x deployment frequency |
| J2EE/EJB Monoliths | Spring Boot microservices with Jakarta EE patterns | Java EE donated to Eclipse Foundation | Shared database schemas, tightly coupled business logic, session state management | Cloud-ready services, independent scaling, gradual decomposition options | Improved system resilience, 60% faster feature delivery |
| Struts 1.x Applications | Spring MVC or React/Angular with REST APIs | Struts 1 EOL, no security patches since 2013 | Critical security vulnerabilities (RCE), UI coupling with business logic | Modern MVC architecture, secure request handling, API-first design | Eliminated security incident risk, improved UI development velocity |
| Struts 2 (Vulnerable Versions) | Spring Boot with modern frontend or API-first architecture | Multiple critical RCE vulnerabilities in older versions | Complex migration of Action classes, interceptor chains, result types | Secure framework with active maintenance, better testability | Reduced compliance audit findings, faster security patch deployment |
| JSP/JSF Applications | Thymeleaf, React, Angular, or Vue.js with REST backends | Tied to Java EE lifecycle, limited modern browser support | Server-side state management, complex component lifecycle, SEO limitations | Modern SPA frameworks, better user experience, mobile-responsive design | Improved customer engagement metrics, faster UI iteration cycles |
| Swing/AWT Desktop Apps | JavaFX, Electron, or web-based applications | Tied to Java SE desktop support lifecycle | Platform-specific deployment, limited cross-platform compatibility | Cross-platform deployment, web-based accessibility, modern UI patterns | Reduced desktop support costs, expanded user accessibility |
| SOAP/JAX-WS Services | REST APIs with Spring Boot or gRPC for high-performance scenarios | Limited modern tooling support, verbose protocols | Complex WSDL dependencies, WS-* standards compatibility, client code generation | Lightweight JSON APIs, better mobile integration, simplified client development | Reduced API latency, improved third-party integration adoption |
| JDBC-Heavy Data Access | Spring Data JPA or Hibernate with connection pooling | Not deprecated but maintenance-intensive | Vendor-specific SQL, manual connection management, limited query optimization | Modern ORM with caching, query optimization, database portability | 40% reduction in database-related production issues |
| Manual Build/Deploy | Maven/Gradle with CI/CD pipelines (Jenkins, GitHub Actions, GitLab) | High operational risk, slow deployment cycles | Legacy build scripts, manual testing procedures, deployment coordination | Automated testing, rollback capabilities, deployment frequency increase | 75% reduction in deployment-related downtime |
Java 17 free Oracle license expired in September 2024. Java 21 free Oracle license expires September 2026. For programs starting in 2026, Java 25 LTS provides the longest available support runway through 2033. Java 26 non-LTS, released March 2026, is not a recommended migration target.
Spring Boot 4.0 and Your Legacy Java Migration Plan
Spring Boot 4.0 shipped in November 2025 and is the current Spring major release. It requires Java 17 minimum, Jakarta EE 11, Jackson 3.x, and Spring Framework 7. These are not incremental changes; each introduces breaking dependencies that compound across the migration path.
Direct migration from Java 8 or Spring Boot 2.x to Spring Boot 4.0 is a multi-step process. The recommended bridge path is Spring Boot 2.7 → 3.5 → 4.0, with corresponding Java version milestones at each step. Spring Boot 3.5 OSS support ends November 2026, making it a bridge version only, not a long-term destination.
For codebases over 500,000 lines of code, the compounding breaking changes across this path make automated dependency mapping essential before starting any transformation. Attempting to manually trace Jackson 3.x compatibility, Jakarta EE 11 namespace requirements, and Spring Framework 7 API changes across a large, undocumented codebase introduces significant rework risk.
A $0 codebase assessment maps your specific dependency chain against Spring Boot 4.0 requirements and delivers a phased migration sequence in 2–5 days. Start your assessment here.
Java 25 LTS vs. Java 21 LTS: Which Version Should US Enterprises Target in 2026?
Java 25 LTS, released September 2025, provides Oracle free support through 2033. Oracle free support for Java 21 expires September 2026, meaning teams targeting Java 21 today will need to re-evaluate their support model within months of completing migration.
For programs initiating in 2026, Java 25 LTS is the recommended target. Organizations mid-migration on Java 21 should continue their current path rather than pivot. The disruption of changing targets mid-project outweighs the support runway difference.
Java 25 delivers production-ready virtual thread improvements and compact object headers that benefit high-volume enterprise applications. Spring Boot 4.0 supports Java 25 and recommends it for new deployments. Java 26 non-LTS, released March 2026, is not a migration target.
Quick Java Migration Checklist
If your applications still rely on Java EE, upgrading to Jakarta EE is a critical first step toward long-term compatibility and cloud readiness. Before you start, make sure these essentials are covered:
Code & Dependency Updates
- Scan for javax.* imports and replaces them with jakarta.* equivalents.
- Update Maven or Gradle dependencies to Jakarta-compatible versions.
- Remove or refactor deprecated Java EE APIs such as JAX-RPC or older EJB patterns.
- If targeting Spring Boot 4.0, validate Jackson 3.x dependency compatibility, Spring Framework 7 alignment, and Jakarta EE 11 baseline requirements before beginning transformation.
Application Server Compatibility
- Confirm server support for Jakarta EE 10+ (e.g., WildFly 27+, Payara 6+, TomEE 9+).
- Validate configurations for JNDI, persistence units, and security realms during server migration.
Build & Testing Validation
- Run automated unit and integration tests to detect namespace or dependency regressions early.
- Check CI/CD pipelines for outdated Java EE references or plugin incompatibilities.
Security & Configuration
- Reassess authentication, authorization, headers, and CORS configurations post-migration.
- Review SSL/TLS certificates and encryption standards against Jakarta runtime defaults.
Tip: Use OpenRewrite 8.x to automate namespace migration from javax.* to jakarta.*, Spring Boot version dependency bumps, and known API deprecation fixes. For legacy codebases with undocumented business logic or custom framework extensions, OpenRewrite handles the predictable mechanical changes while AI-native comprehension is required for the remaining 30–40%.
What Are the Biggest Risks in Java Migration?
Even with strong executive sponsorship and an adequate budget, Java migrations fail when specific technical and operational risks aren’t addressed up front. These are the most common failure modes and their business impact.
1. Hidden Dependencies & Technical Debt
Legacy codebases routinely contain undocumented API calls between services that only surface during load testing, alongside:
- Shared database schemas that create cascading failures during service extraction
- Custom framework extensions built on deprecated Java EE APIs
- Legacy JAR dependencies with transitive security vulnerabilities
Business Impact: Project timeline extensions of 3–6 months, budget overruns averaging 40%, and potential service outages during cutover.
2. Application Server Migration Complexity
- WebLogic/JBoss-specific features (JCA connectors, proprietary clustering, custom security realms)
- JNDI dependencies hardcoded throughout the application layers
- Container-managed transactions that don’t directly translate to Spring’s transaction model
- Deployment descriptor complexity spanning multiple XML configuration files
Business Impact: Functional regression during migration, extended testing phases, and potential loss of enterprise features.
3. Framework Incompatibility Gaps
- Struts Action classes with complex inheritance hierarchies requiring a complete rewrite
- JSF component trees with custom renderers that have no modern equivalent
- EJB session beans with stateful business logic difficult to extract cleanly
- Legacy Spring configurations (XML-based) that conflict with modern annotation approaches
Business Impact: Feature parity gaps, user experience degradation, and extended development cycles.
4. Data Migration & Performance Risks
- ORM mapping changes from Hibernate 3/4 to modern versions, causing query performance regression
- Database connection pooling behavior changes affecting transaction isolation
- Caching strategies that don’t translate to cloud-native environments
- Batch processing jobs with timing dependencies on legacy scheduler integration
Business Impact: System performance degradation, data consistency issues, batch processing failures.
5. Security & Compliance Gaps
- Authentication model changes from JAAS to modern OAuth2/OIDC requiring user migration
- Audit logging formats that don’t meet regulatory requirements in the new framework
- Session management changes affecting single sign-on integration
- Encryption key management during transition between legacy and modern systems
Business Impact: Compliance audit failures, security incidents during transition, and user access disruption.
For leadership teams, these risks translate directly into schedule variance, budget overruns, and business continuity threats. The key insight: these risks are predictable and addressable during planning, but expensive and disruptive when discovered mid-project.
Successful Java migrations implement risk mitigation as part of the architectural design process, not as reactive firefighting.
Best Practices for a Successful Java Migration
Migrating legacy Java applications is complex, spanning frameworks, servers, and runtime environments that have evolved over decades. The following best practices, drawn from large-scale enterprise modernization programs, help ensure a smooth, verifiable transition.
1. Establish an accurate baseline of your legacy stack
Automate code and dependency discovery across application servers, frameworks, and libraries. In most Java portfolios, 25–40% of actual dependencies remain undocumented until deep analysis is performed.
2. Prioritize modernization by business value, not code size
Start with high-impact modules that are loosely coupled and easier to containerize. This approach accelerates validation and creates quick wins while minimizing disruption.
3. Decouple from application servers early
For WebLogic, JBoss, or GlassFish workloads, isolate business logic from vendor-specific APIs before migration. This simplifies redeployment to Spring Boot or Jakarta EE environments. Decoupling also eliminates $500K–$2M or more in annual licensing — a hard-dollar saving that frequently funds the modernization program itself and is the most immediately quantifiable ROI driver for US enterprise buyers.
4. Choose modernization patterns strategically
Apply refactor, replatform, or re-architect patterns based on module criticality. Monoliths often benefit from a strangler pattern, while stable services can be containerized directly.
5. Maintain functional parity checkpoints
Automate regression testing after each migration phase to confirm behavior consistency between legacy and modernized modules. This reduces risk and rebuilds confidence early.
6. Embed DevSecOps and CI/CD pipelines from day one
Integrate build, test, and deployment automation as soon as modernization begins. Continuous validation prevents integration drift and shortens release cycles.
7. Combine AI automation with human oversight
Leverage Gen AI for code translation, dependency mapping, and documentation generation, but validate business logic through experienced engineers. This hybrid model ensures both speed and reliability.
How Gen AI Automates Java Migration and Where Human Oversight Remains Essential
Enterprise Java migration fails most often because of incomplete dependency discovery, missed business logic patterns, unverified refactoring, and high-risk big-bang deployments. Legacy code complexity is just one dimension of this challenge.
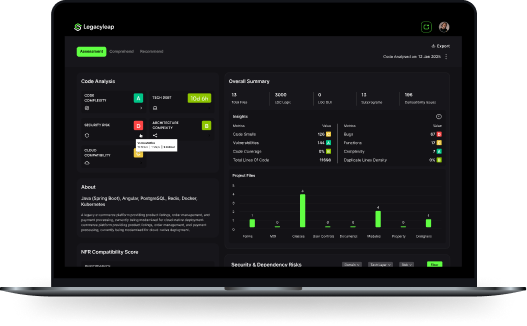
Legacyleap’s platform addresses these systematic gaps by embedding compiler-grade Gen AI capabilities into every phase of modernization, while preserving the development workflows and governance standards your teams already follow.
| Phase | Traditional Challenges | Legacyleap Gen AI Capability | Business Impact |
| 1: Comprehend & Assess | Manual code archaeology, tribal knowledge gaps, undocumented business rules embedded in 15+ year old codebases | Codebase comprehension agents map architecture patterns, extract business logic, trace data flows, and identify unused code across J2EE, Struts, JSP, EJB, and custom framework combinations | Discovery time reduced from months to weeks; eliminates “surprise complexity” that destroys project budgets |
| 2: Recommend | Migration estimates based on high-level assumptions; risks and blockers surface during development causing timeline slips | Automated migration path analysis with quantified complexity scoring, test coverage gap identification, and refactoring-ready code extraction with business impact assessment | Data-driven budget and timeline forecasts that hold up under executive scrutiny; early mitigation of project killers |
| 3: Modernize | Rewrite-heavy approaches that discard years of business logic refinement; manual refactoring prone to introducing bugs | Business logic preservation workflows that extract domain rules from legacy frameworks and apply modern architectural patterns while maintaining functional equivalence, including Spring Boot 4.0 compatibility transformations, Jackson 3.x dependency resolution, and Jakarta EE 11 migration | 60% faster code transformation with verifiable business logic continuity; reduced developer burnout from manual refactoring |
| 4: Validate | Limited test automation leaving critical user workflows unverified; manual QA that misses edge cases refined over years of production use | Comprehensive test generation including unit, integration, and behavioral tests that capture existing system behavior patterns for regression prevention | Near-complete verification coverage before deployment; 80% reduction in post-cutover defect rates |
| 5: Deploy | High-risk big-bang releases with limited rollback options; slow stabilization periods with manual issue resolution | Intelligent deployment orchestration with automated health monitoring, performance benchmarking, and rollback triggers integrated with existing CI/CD pipelines | Predictable, low-risk cutovers with measurable stability improvements and automated recovery capabilities |
Why This Matters for Java Migration ROI
Instead of adding another “tool” to manage, Legacyleap functions as an intelligence amplification layer across your existing Java modernization process, without disrupting established development workflows or governance procedures.
Measurable outcomes:
- Timeline predictability that survives executive review and budget cycles
- Risk reduction through automated discovery and verification
- Cost control by eliminating surprise complexity and rework cycles
- Business continuity through graduated deployment and rollback capabilities
For a deeper look at how Gen AI powers each phase of a modernization program, see How Can Gen AI Drive Every Step of Your Modernization Journey?
Java Modernization Patterns & Legacyleap’s Approach
Not every Java migration follows the same technical path. While the stack mapping shows component-level transitions, executives benefit from understanding migrations grouped by architectural pattern. This enables better resource allocation, timeline forecasting, and risk management across the modernization portfolio.
Below are the four dominant Java modernization patterns we encounter, with their specific challenges and how Legacyleap’s Gen AI approach addresses them systematically.
1. Monolith Decomposition
Typical stacks: Java EE monoliths on WebLogic/JBoss, tightly-coupled EJB architectures, shared database schemas across business domains.
Common challenges:
- Business logic scattered across EJB session beans, DAOs, and JSP presentation layers
- Database schemas with complex foreign key relationships preventing clean service boundaries
- Transaction boundaries that span multiple business domains requiring distributed transaction coordination
- Shared caching layers and JMS message handling that create hidden service dependencies
Legacyleap approach:
- AI-powered service boundary identification using business domain analysis and data flow mapping to suggest optimal microservice extraction points
- Gradual strangler fig migration that preserves system stability while incrementally extracting services
- Database decomposition planning with automated schema analysis
- Transaction boundary preservation ensuring ACID compliance is maintained during service extraction
Business impact: Enables independent service scaling and deployment while preserving critical business logic and data consistency requirements.
Case Study: EJB3 Systems Modernization
A leading transportation technology company partnered with Legacyleap to modernize a legacy EJB3-based monolith into Spring Boot microservices.
Through compiler-grade AI comprehension and AWS-native automation, the team:
- Reduced code-comprehension time by 50% using automated dependency and relationship mapping.
- Leveraged Amazon Bedrock for intelligent code analysis and Amazon Neptune for architectural graph modeling.
- Achieved 60–70% automation in refactoring to Spring Boot microservices with complete regression validation.
The result was a modular, cloud-ready architecture that improved development velocity and resilience, delivered without interrupting ongoing business operations.
2. Framework Modernization
Typical stacks: Struts 1.x/2.x applications, JSP/JSF user interfaces, Spring 2.x/3.x with XML configuration.
Common challenges:
- Action classes with complex inheritance hierarchies and tightly coupled presentation logic
- JSF component trees with custom renderers and validators that have no modern framework equivalent
- Legacy Spring XML configurations mixed with annotation-based dependency injection creating configuration conflicts
- Custom tag libraries and JSP scriptlets with embedded business rules
Legacyleap approach:
- Framework pattern recognition that identifies reusable business logic within presentation layer components
- Automated MVC extraction that separates concerns and creates clean API boundaries for modern frontend integration
- Configuration modernization that converts XML-based Spring configurations to annotation and Java-based configuration
- Component library migration that maps legacy UI components to modern framework equivalents while preserving user experience
Business impact: Modernizes user interface and API layers while preserving complex business rules and user workflow patterns that took years to refine.
3. Infrastructure Platform Migration
Typical stacks: On-premises WebLogic/JBoss deployments, manual build and deployment processes, traditional monitoring and logging.
Common challenges:
- Application server-specific features (JNDI, JCA, proprietary clustering) that don’t exist in containerized environments
- Manual deployment processes with complex coordination between database updates, configuration changes, and application rollouts
- Legacy monitoring tools that provide limited visibility into distributed system behavior
- Security models based on application server realms and database authentication
Legacyleap approach:
- Cloud-native refactoring that extracts application server dependencies and replaces them with Spring Boot embedded server patterns
- Containerization strategy that packages applications with their dependencies while maintaining configuration externalization
- CI/CD pipeline generation that automates build, test, and deployment processes with integrated quality gates
- Observability integration that implements modern logging, metrics, and tracing without requiring application code changes
Business impact: Eliminates application server licensing costs while improving deployment velocity and system observability for better operational control.
4. Data Platform Modernization
Typical stacks: Direct JDBC with custom connection management, legacy Hibernate configurations, stored procedure-heavy architectures.
Common challenges:
- Hand-written SQL with database-specific syntax that prevents cloud database migration
- Custom ORM configurations that rely on deprecated Hibernate features not available in modern versions
- Stored procedures containing critical business logic that can’t be easily extracted to application layers
- Connection pooling and transaction management tuned for single-server deployments
Legacyleap approach:
- ORM modernization that upgrades Hibernate configurations while preserving query performance characteristics
- Database abstraction that extracts database-specific SQL into portable query implementations
- Stored procedure refactoring that identifies business logic suitable for extraction to service layers
- Connection management optimization for cloud-native deployment patterns with auto-scaling capabilities
Business impact: Enables cloud database adoption while preserving years of performance tuning and business logic refinements embedded in data access layers.
Why Pattern-Based Planning Matters for Executives
Grouping Java migrations by architectural pattern converts complex technical decisions into manageable portfolio planning:
- Resource allocation becomes predictable when similar migration patterns are grouped together
- Timeline forecasting improves when teams can leverage lessons learned across similar architectural challenges
- Risk management enables proactive mitigation strategies based on pattern-specific failure modes
- ROI measurement can be standardized across migrations following similar patterns
See exactly how Legacyleap’s Gen AI-driven approach applies to each type of migration, building confidence in delivery outcomes.
Java Modernization in US Regulated Environments: HIPAA, SOC 2, PCI-DSS, and FDA 21 CFR Part 11
Introducing AI into mission-critical Java modernization raises legitimate concerns about code security, intellectual property protection, and compliance with enterprise governance standards.
For US enterprises in regulated industries, these concerns carry direct audit and liability implications that must be addressed as part of the migration architecture, not as an afterthought.
Compliance Considerations for US Regulated Environments
- HIPAA (Healthcare) Java systems processing protected health information (PHI) must maintain audit trail integrity throughout migration. Authentication model changes, particularly transitions from JAAS to OAuth2/OIDC, require documented validation that access controls remain intact at every migration stage. AI-assisted transformation workflows must log all code changes with engineer approval records to satisfy HIPAA audit requirements. Legacyleap’s human-in-the-loop governance model ensures no AI-generated change is committed without explicit engineer sign-off, creating the audit trail HIPAA auditors require.
- SOC 2 (Service Organizations) SOC 2 Type II compliance requires continuous evidence of access controls, change management procedures, and system availability. A Java migration that introduces uncontrolled AI-generated code changes, undocumented dependency updates, or gaps in version history creates audit exposure. Legacyleap’s governance layer automatically maintains change logs with approval records, keeping SOC 2 evidence collection continuous rather than reactive.
- PCI-DSS (Payment Card Industry) Systems handling cardholder data face strict requirements around encryption standards, access logging, and vulnerability management. Migrating off Java 8 directly addresses PCI-DSS Requirement 6.3, which mandates that all system components are protected from known vulnerabilities. Remaining on unpatched runtimes is not a defensible position in a PCI-DSS audit. Post-migration, Legacyleap integrates with enterprise security scanning tools (SonarQube, Veracode, Checkmarx) to maintain continuous vulnerability detection across the modernized codebase.
- FDA 21 CFR Part 11 (Life Sciences & Medical Devices) For US life sciences organizations and medical device manufacturers, 21 CFR Part 11 governs electronic records and signatures in FDA-regulated workflows. Java systems embedded in clinical or manufacturing processes must demonstrate that modernization did not alter system behavior in ways that affect validated workflows. Legacyleap’s automated parity testing generates evidence of functional equivalence between legacy and modernized systems, documentation that directly supports 21 CFR Part 11 revalidation processes.
Note: For US organizations with European operations, GDPR data residency and processing requirements apply as a secondary compliance layer. Legacyleap’s regional cloud deployment model supports GDPR data residency requirements alongside US compliance frameworks.
Security Architecture
- AI Gateway Control Layer: All AI interactions are routed through a secure, private gateway that enforces authentication, authorization, and request filtering. Customer code never reaches public AI endpoints or shared model instances.
- Data Residency & Tenant Isolation: AI models operate within your designated cloud region with strict tenant isolation. No code or metadata crosses tenant boundaries or leaves your security perimeter.
- Encryption Standards: All data in transit and at rest uses enterprise-approved encryption (TLS 1.2+, AES-256). Code analysis and transformation occur within encrypted processing environments.
- Compliance Integration: Workflows automatically maintain audit trails for HIPAA, SOC 2, PCI-DSS, and FDA 21 CFR Part 11. All AI-assisted changes are logged with engineer approval records.
Governance & Control
- Human-in-the-Loop Architecture: AI generates recommendations and code transformations, but engineers maintain approval authority for all changes. Nothing is automatically committed or deployed without explicit human verification.
- Granular Data Processing: Only specific code segments required for individual AI tasks are processed, minimizing data exposure. Full codebase analysis is performed through incremental, controlled processing.
- IP Protection: Code patterns and business logic remain within your security boundary. AI models learn general refactoring patterns without retaining customer-specific code or business rules.
Enterprise Integration
- Existing Security Tool Integration: Legacyleap integrates with enterprise security scanning tools (SonarQube, Veracode, Checkmarx) to maintain existing vulnerability detection workflows.
- Access Control Integration: Platform access integrates with enterprise identity management (Active Directory, LDAP, SAML), maintaining existing role-based access control patterns.
- Audit & Compliance Reporting: Automated generation of compliance reports showing AI-assisted changes, engineer approvals, and security validation results for regulatory review.
Bottom line: AI acceleration operates as a controlled augmentation layer that enhances engineer productivity while maintaining the same security, privacy, and compliance standards as your core development infrastructure.
For a full overview of Legacyleap’s security architecture and on-premises deployment model, see the security and privacy documentation.
Conclusion: Moving from Legacy Risk to Strategic Advantage
Java modernization in 2026 is a strategic repositioning for AI-enabled business capabilities.
US enterprises running on Java 7/8, J2EE, or legacy framework stacks aren’t just managing technical debt. They’re accepting increasing operational risk while constraining their ability to integrate AI-powered features that are rapidly becoming competitive requirements across industries.
The modernization imperative is now clear:
- Support timelines have compressed from “someday” to “this budget cycle”
- Security risks are quantifiable and increasing with each unpatched vulnerability
- Talent availability is declining while compensation premiums for legacy skills are rising
- Cloud economics favor modern architectures that can scale efficiently and integrate with AI platforms
The patterns, risk frameworks, and ROI analysis provided here give leadership teams the strategic planning tools needed to approach Java modernization as a controlled business transformation rather than a disruptive technical project.
Legacyleap’s Gen AI-powered approach ensures migration execution that’s faster, safer, and more predictable than traditional manual approaches, while preserving the business logic and operational stability that legacy systems provide.
The strategic choice is straightforward: Modernize proactively with controlled timelines and predictable outcomes, or accept increasing operational risk while competitors gain AI-enabled advantages.
Claim a $0 Java Codebase Assessment
If your team is running Java 8, J2EE, Struts, JSP/JSF, or WebLogic/JBoss, we’ll scan a portion of your codebase and deliver a complete modernization picture — in 2–5 days, at no cost, with all processing inside your environment.
What You’ll Receive:
- Functional & Technical documentation
- Architecture diagrams
- API references & integration maps
- Risk & complexity heatmap
- Modernization Timelines & Estimate
- Full Modernization Plan
FAQs
A Java upgrade moves from one runtime to another, for example, Java 8 to Java 17, with minimal code changes and the same frameworks and servers in place. A Java migration modernizes the full stack: frameworks, application servers, and architecture, such as moving from EJBs on WebLogic to Spring Boot with Jakarta EE and containers. Migration demands deeper refactoring, comprehensive testing, and CI/CD and security updates that a version upgrade alone does not require.
For programs initiating in 2026, Java 25 LTS is the recommended target. Released September 2025, it carries Oracle free support through 2033, the longest available support runway. Oracle free support for Java 21 expires September 2026, meaning teams targeting Java 21 today face an immediate support re-evaluation on completing migration. Organizations already mid-migration on Java 21 should continue rather than pivot. Java 26 non-LTS, released March 2026, is not a migration target.
Spring Boot 4.0 requires Java 17 minimum, Jakarta EE 11, Jackson 3.x, and Spring Framework 7, none of which are incremental changes from a Java 8 or Spring Boot 2.x baseline. Direct migration to Spring Boot 4.0 from that starting point requires a phased path through Spring Boot 3.5, with validation checkpoints for each breaking dependency. Spring Boot 3.5 OSS support ends November 2026, making it a bridge version only. For large codebases, automated dependency mapping before starting transformation is essential to avoid compounding rework.
Timelines vary by system size and complexity. A mid-sized enterprise application can often be modernized in 3–6 months with automation, while large portfolios may take 12–18 months when phased across multiple systems. AI-assisted refactoring and dependency tracing significantly shortens these timelines.
Delaying migration increases security risk, compliance exposure, and operational costs. Unsupported runtimes become prime targets for breaches, audit failures can result in multimillion-dollar fines, and maintenance of legacy skills becomes increasingly expensive. In many cases, ongoing support and infrastructure costs exceed the one-time cost of migration.
No. Most Java migrations can be completed through a refactoring-first approach, which preserves existing business logic while modernizing frameworks, servers, and build systems. Full rewrites are risky, costly, and rarely necessary unless the system is fundamentally unsalvageable.
Best practices include phased cutovers using the Strangler Fig pattern, parallel runs of old and new systems until parity is validated, automated regression testing, and CI/CD pipelines with rollback capabilities. These strategies allow modernization without disrupting ongoing business operations.
References
[1] Oracle Java SE Support Roadmap —https://www.oracle.com/java/technologies/java-se-support-roadmap.html
[2] Oracle Java SE 7 End of Extended Support —https://blogs.oracle.com/java/java-se-7-end-of-extended-support-in-july-2022
[3] Jakarta EE —https://jakarta.ee/